可移除Media 漏洞威脅企業營運
資料對本組織的運作至關重要。在整個網路層級及高風險區域中,皆需仰賴資料與系統檔案來支援營運、安全及其他關鍵任務,且在許多情況下,這些資料必須在物理隔離的環境間進行傳輸。在核能環境中,隔離是一項至關重要的安全管控措施,有助於維持運作完整性,同時保護人員、資產及環境。
在我們的環境中,可移除式儲存媒體與臨時裝置是連接安全區域與可信度較低區域之間不可避免的通道,藉此執行更新與診斷作業。
營運技術(OT)網路安全與網路保障主管
為了符合安全規範並保護環境,該組織過去仰賴多項人工檢查及傳統程序,其中包含人員監督與文件記錄。
有幾個關鍵問題需要解決:
檔案安全
惡意檔案可能潛入核設施,並破壞其安全運作。供應鏈風險——包括遭篡改的軟體、被修改的韌體以及受損的第三方資料——將進一步增加遭受網路入侵及潛在破壞活動的風險。
可移除Media
USB 、SD 卡及類似裝置可能引入惡意軟體、導致未經授權的資料外洩,並繞過現有的網路安全防護措施。此外,它們還會造成稽核上的困難,並對儲存於可移除媒體上的內容完整性構成風險。
瞬態裝置風險
筆記型電腦、維護設備及承包商系統在連接到安全網路時,可能會引入威脅、未經驗證的設定或隱藏的存取路徑。
核能監管
遵守嚴格的法規要求,是確保在檔案安全與可移除媒體保護方面建立堅實的營運及網路安全防護措施的核心驅動力。在核能領域,這不僅僅是法規遵循的問題。各組織有責任維持最高等級的安全防護,因為即使是微小的中斷或偏差,都可能對安全、環境及國家安全造成重大影響。
營運流程
過去,該組織的各設施在運作上採用了不盡相同的流程、供應商及傳統做法。由於需進行多次人工檢查,使得在維持品質與合規性的同時,難以擴展流程規模。員工經常需要親自掃描並在龐大的設施內來回運送媒體數次,這不僅造成延誤與作業疲勞,更增加了人為錯誤的風險。各團隊亟需一套標準化的方法,以便在所有據點一致地實施。
針對進入運作環境的檔案所實施的手動釋放控制,雖有助於防止疫情爆發,卻也增加了額外負擔,並提高了關鍵安全與防護流程中發生錯誤的風險。
加強全球監管
當檔案跨越所有邊界時,我們需要對其擁有更強的管控能力、安全性及可視性。我們需要將現有程序現代化並加以簡化,同時協調目前已實施的許多流程。
營運技術(OT)網路安全與網路保障主管
管理層已認定,對現有流程進行現代化、簡化及更完善的協調是勢在必行的。為應對這些挑戰,該組織選擇了OPSWAT 其整合式平台提供了一套全面的解決方案,能夠在整個運作環境中保護檔案、可移除媒體及臨時裝置的安全。
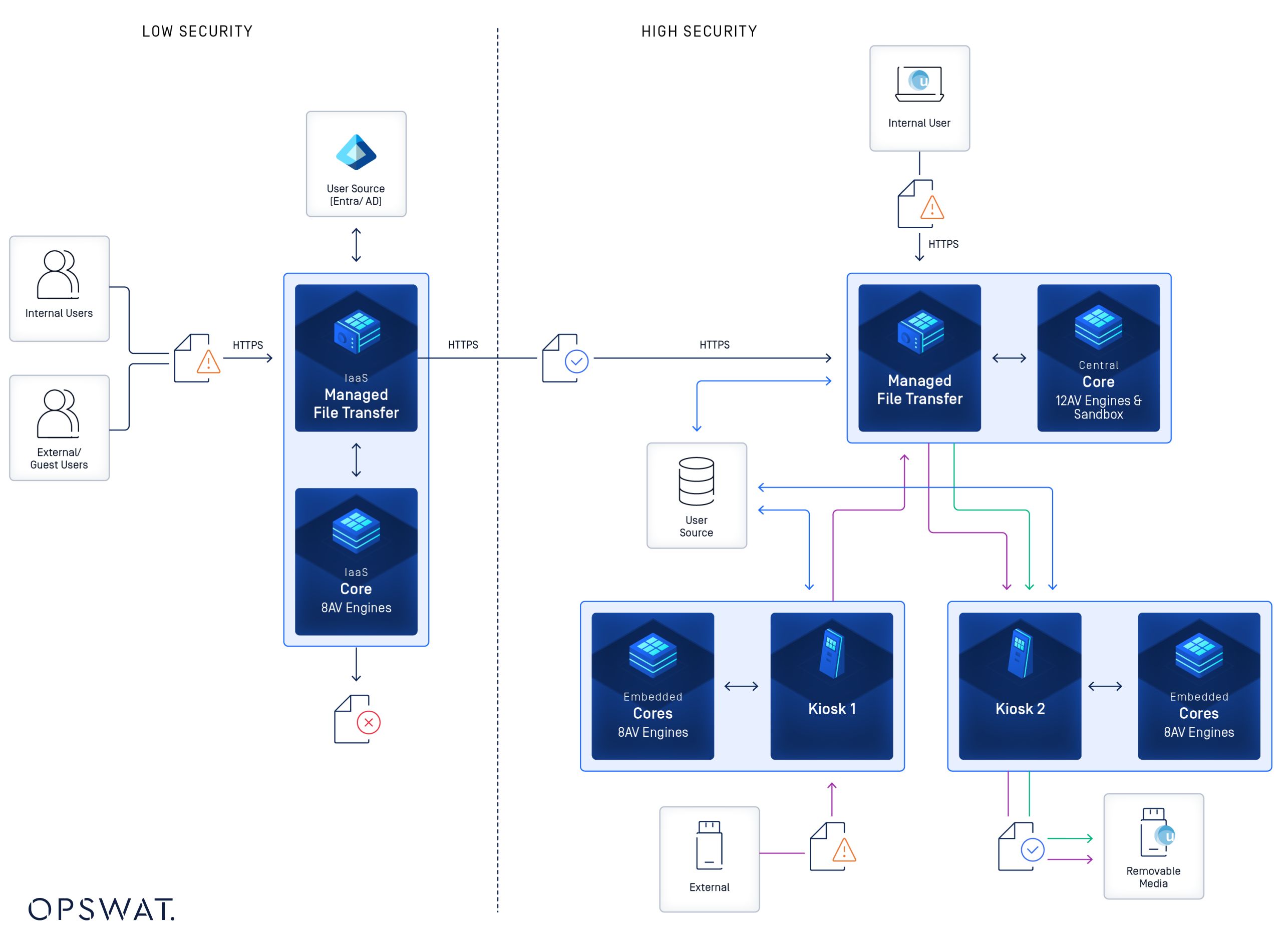
透過在全球所有設施部署整合式的OPSWAT 該組織確保所有進入核能環境的檔案均須經過零信任檢查流程。無論來源或進入點為何——無論是可移除媒體、臨時裝置、現場人員或外部第三方——所有檔案都會經過多層次防禦控制機制處理,以偵測針對其環境的已知與未知威脅。

此目標是透過在既定的檢查點部署MetaDefender (作為整合式「羊圈」解決方案)及MetaDefender 在可移除媒體與臨時裝置進入環境前進行掃描而達成的。
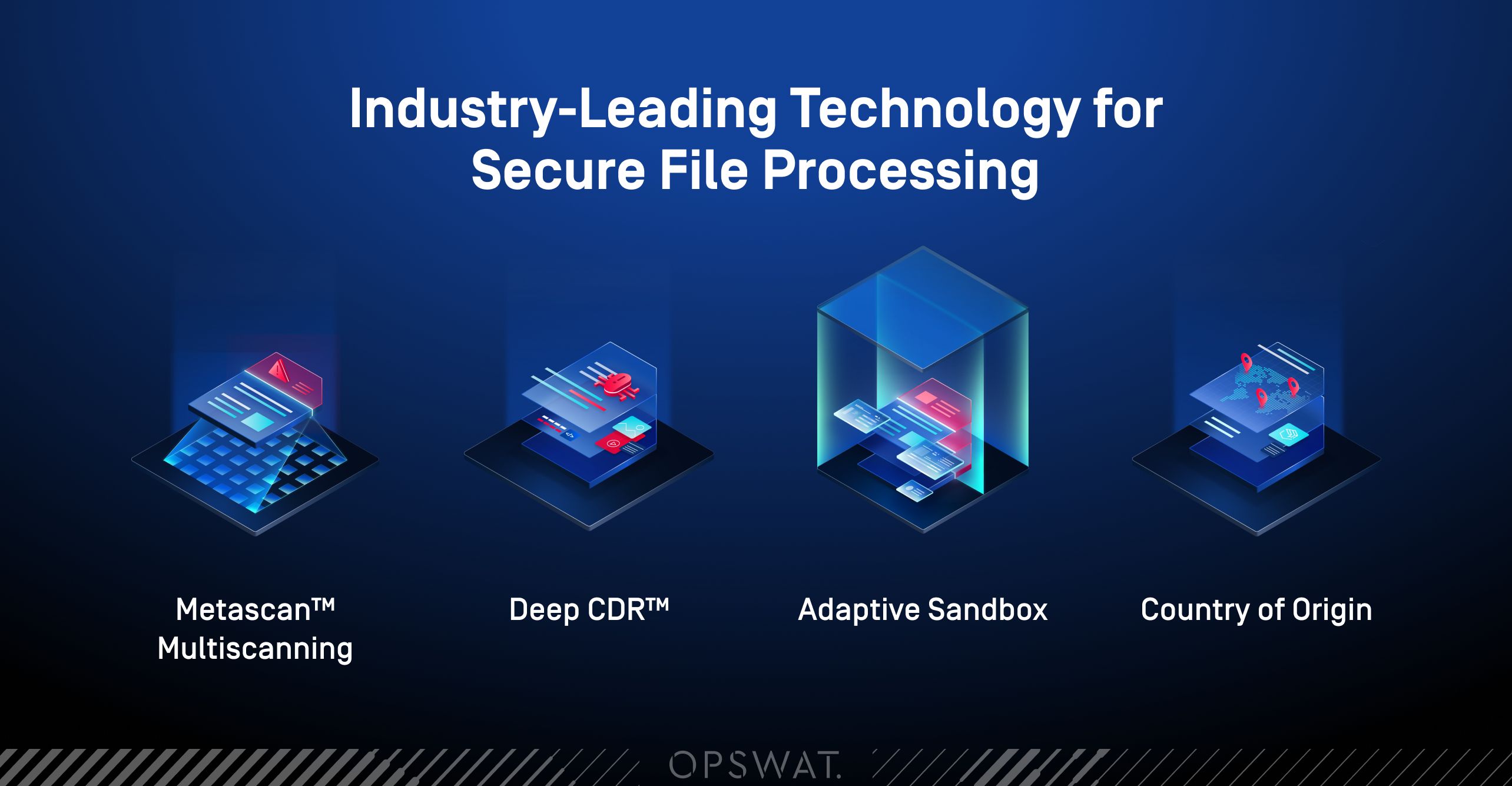
每項解決方案皆運用一套強大的技術組合,以防止惡意內容進入環境,其中包括:
- 使用多個反惡意軟體引擎進行Multiscanning
- 完整檔案檢視與擷取
- 深度CDR™技術
- 原產地檢查
- 檔案漏洞掃描
- 智慧型聲譽管理服務
這種多層次的方法在確保符合所需效能水準的同時,也落實了統一的檔案安全標準,即使在掃描過程中啟用了多個引擎,仍能維持運作效率。
每個人的工作已經夠辛苦了,何況還要花半小時等待USB 掃描。但OPSWAT 這樣,即使啟用多個引擎,其強大的後端套件仍能維持高效運作。
營運技術(OT)網路安全與網路保障主管
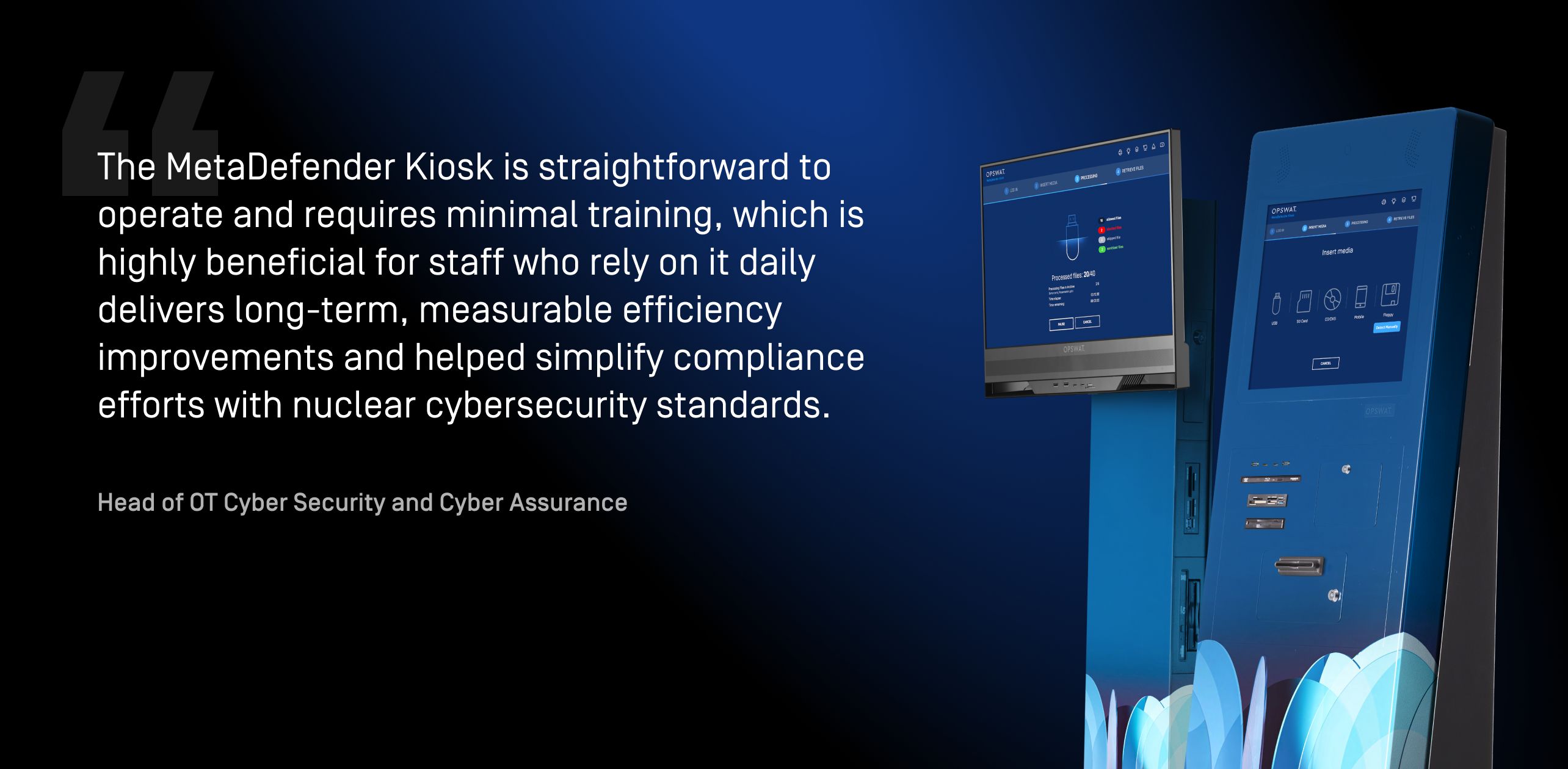
MetaDefender Kiosk 所有可移除儲存媒體Kiosk 快速且可靠的驗證,從而彌補了USB 周邊的一項重大安全漏洞。MetaDefender Drive 作為供應鏈保障工具,用於在授予存取權限前掃描供應商的筆記型電腦。
透過MetaDefender Endpoint我們已消除基於信任的假設,確保僅允許經過核准的加密 USB 裝置,以及經過掃描、未經篡改的乾淨檔案存取關鍵終端裝置。
營運技術(OT)網路安全與網路保障主管
OPSWAT 的OPSWAT 透過獨立式與mobile 兩種形式,提供協調且靈活的掃描功能,能無縫融入企業與資安工作流程。
核心能力:
- 集中管理以實現一致的部署與控制
- 可靈活調整以適應營運需求的自助服務亭格式
- 跨所有環境的精簡稽核與可視性
- 輕鬆實施,僅需最低限度的培訓
- 縮短新用戶與團隊的入職時間
花費數分鐘執行掃描,能顯著降低發生嚴重系統問題的風險。相較於可能耗費數週時間從重大故障中恢復,這短暫的掃描時間實屬微不足道的付出。
營運技術(OT)網路安全與網路保障主管
此次部署獲得了整個組織的強力支持,從第一線團隊到高層領導皆然。
擴大戰略夥伴關係
該組織擴大對OPSWAT 的投資OPSWAT MetaDefender File Transfer™ 解決方案,以提升用戶日常任務的效率並降低營運風險。
檔案將透過USB 、內部檔案傳輸及第三方上傳等方式匯入MFT會持續對這些檔案進行威脅掃描,任何可疑檔案都將在解決方案的內建沙箱功能中進行模擬執行。
透過實施額外的技術管控措施(例如版本管理與主管核准),將確保在授予檔案存取權限或跨網域安全傳輸檔案之前,已落實疫情防範措施。
該解決方案將作為一個安全的全球檔案交換平台,供內部團隊與外部合作夥伴使用,既能確保安全以支援業務運作,同時也能提升生產力。
OPSWAT 的合作夥伴OPSWAT 我們在全球核能營運中保護與管理檔案的方式,賦予我們所需的控制力、可視性與一致性。我們期待見證這段關係將引領我們走向何方,以及它如何持續強化我們的協作關係。
營運技術(OT)網路安全與網路保障主管
秉持著保護全球關鍵基礎設施的使命OPSWAT整合式解決方案能守護敏感的 IT 與 OT 環境免受網路攻擊,確保營運連續性,並協助符合法規要求。若想進一步了解這些解決方案,以及它們如何保障關鍵基礎設施網路的安全,請立即聯繫專家。





