在企業
信任邊界之間Secure 傳輸Secure
透過政策驅動的控制措施、深度檢測以及符合
合規要求的治理機制,保護敏感資料在IT、OT、雲端及合作夥伴環境間傳輸時的安全性。
- 跨網域保護
- 基於風險的控制措施
- 合規對齊

OPSWAT 獲得以下機構的信賴
為何企業檔案傳輸會帶來隱藏風險
檔案傳輸繞過安全邊界
檔案經常在使用者、網路、雲端平台及作業系統之間傳輸,卻未經深入檢查,導致惡意軟體、零日漏洞利用程式及嵌入式有效載荷得以在未被察覺的情況下跨越信任區域。

檔案工作流程中的稽核缺口
組織必須證明其能有效管控檔案的存取、傳輸、審核及儲存方式。彼此脫節的工具會導致政策執行與法規申報方面出現盲點。

IT–OT 與跨領域暴露
在受監管及工業環境中,不同安全域之間的檔案交換會帶來風險。若未進行內建的檢查與強制執行,基於檔案的威脅便可能在系統間橫向擴散。
針對
企業檔案傳輸的安全嵌入式解決方案
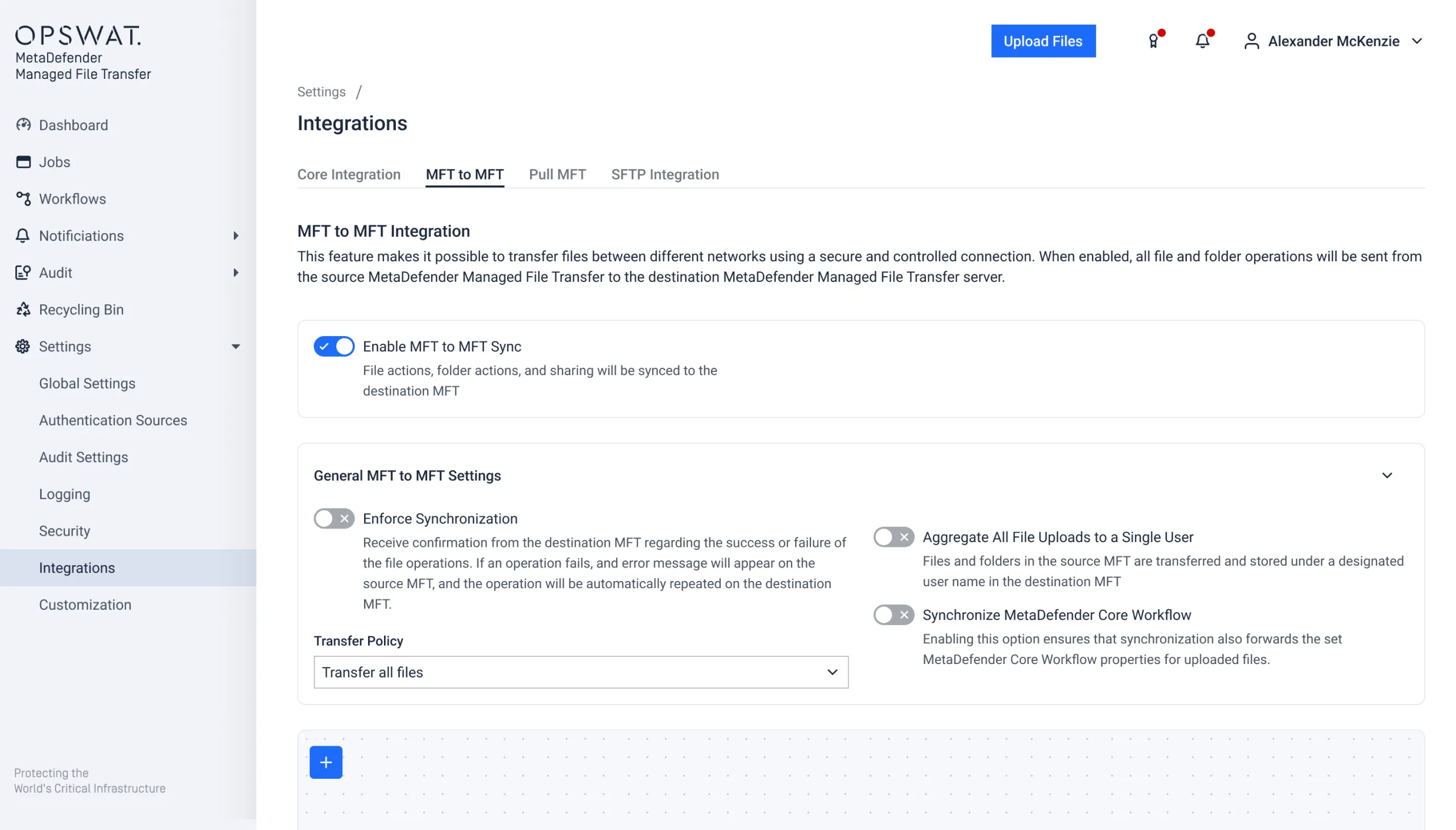
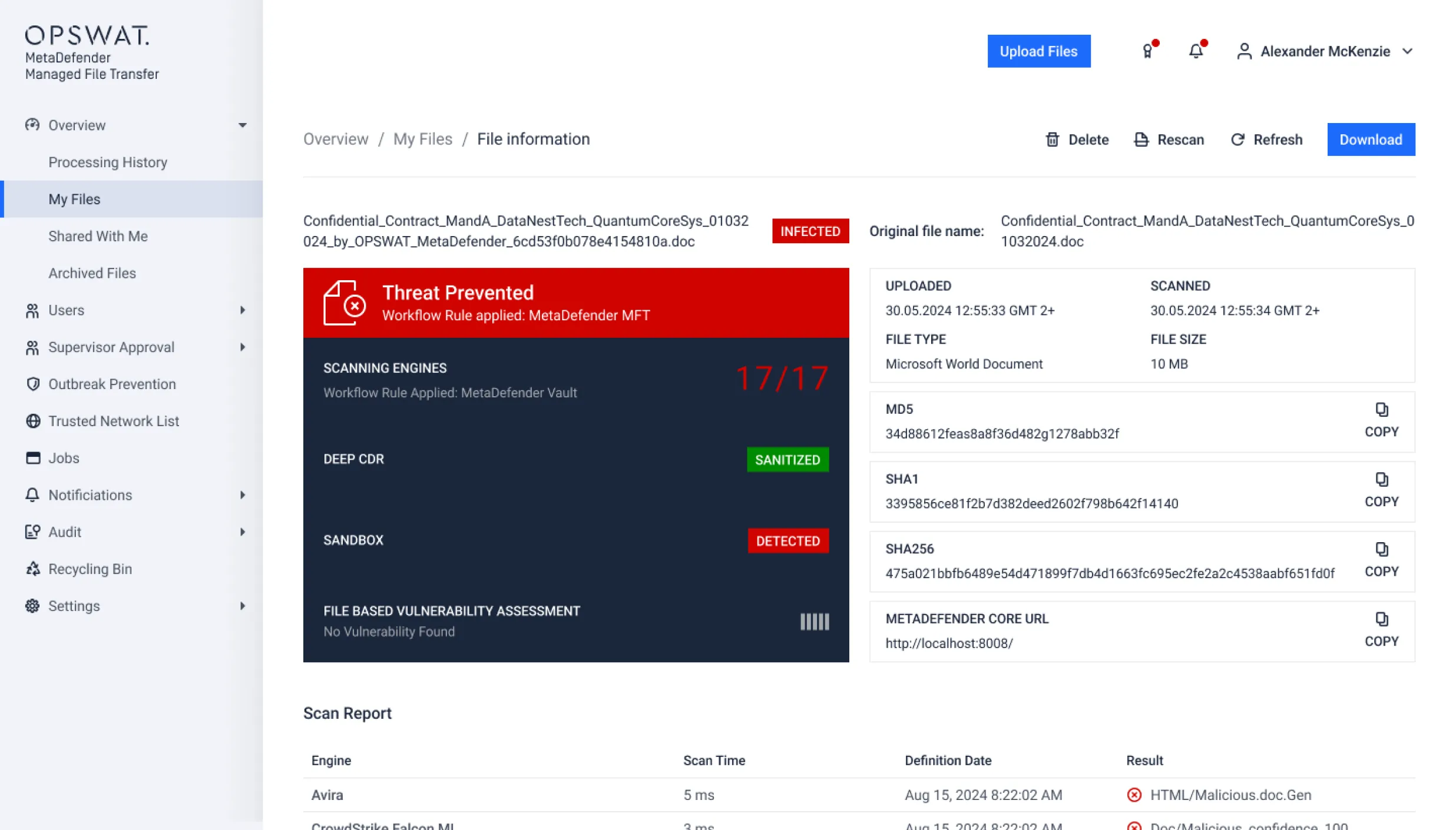
OPSWAT 透過MetaDefender Managed File Transfer MFT)OPSWAT 組織在跨信任邊界進行檔案交換時確保安全性。該解決方案結合了內建檢查、政策執行與集中式治理功能,並運用 Predictive Alin AI 驅動的人工智慧惡意軟體偵測技術,能在檔案傳輸前預先偵測基於檔案的零日威脅。
主要特點
跨網域檔案控制
透過預先定義的信任政策,管控檔案在低安全級別與高安全級別環境間的移動,確保敏感或未經信任的檔案無法繞過安全檢查點。
基於風險的工作流程執行
根據檢查結果(包括由人工智慧驅動的惡意軟體偵測、元資料分類及組織政策)自動執行檔案路由決策,藉此減少人為錯誤並落實一致的治理措施。
分段式環境支援
在企業資訊科技、營運技術(OT)、雲端及合作夥伴生態系統中實施一致的管控措施,以降低跨安全領域的橫向移動風險。
- MetaDefender Managed File Transfer
- MetaDefender Managed File Transfer
- MetaDefender Managed File Transfer
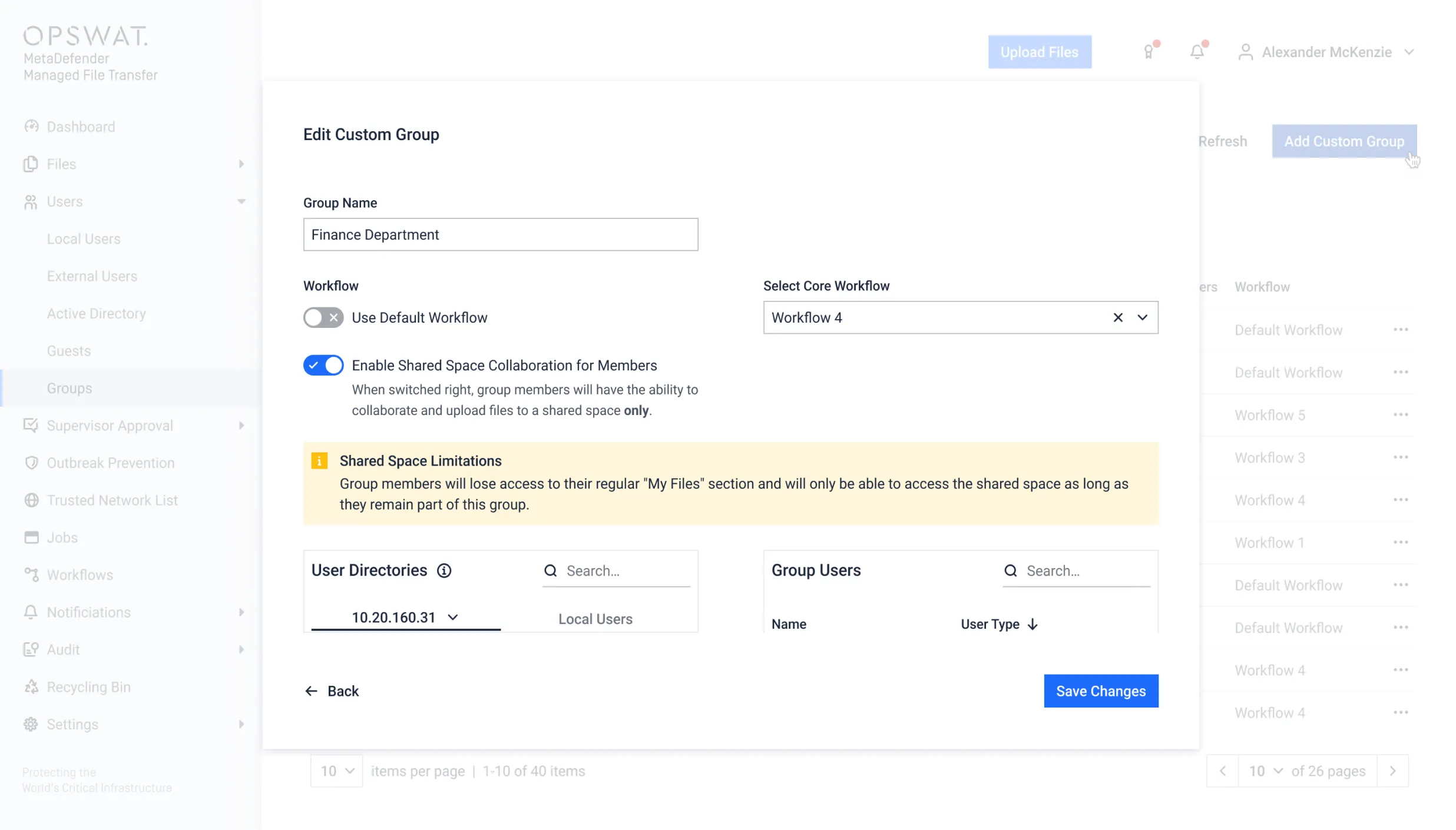
集中式政策治理
透過統一的政策管理與稽核可視性,在各業務單位、子公司及全球營運中實現執法標準化。
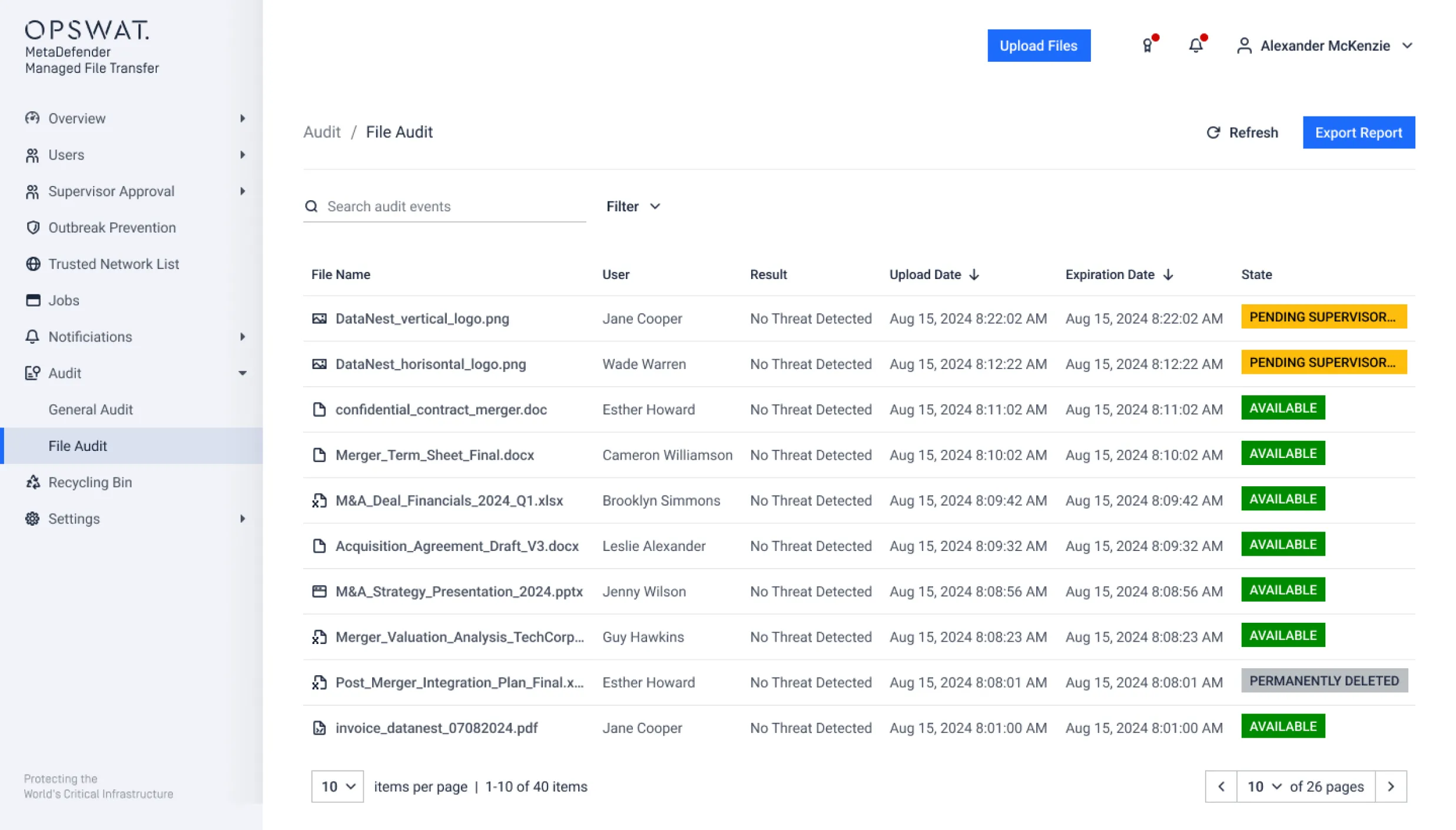
全面的稽核記錄
建立完整的檔案活動與執法決策紀錄,以符合 HIPAA、GDPR、NIS2、PCI、FISMA 及 NIST 等規範框架。
- MetaDefender Managed File Transfer
- MetaDefender Managed File Transfer
親眼見證MetaDefender Managed File Transfer 運作
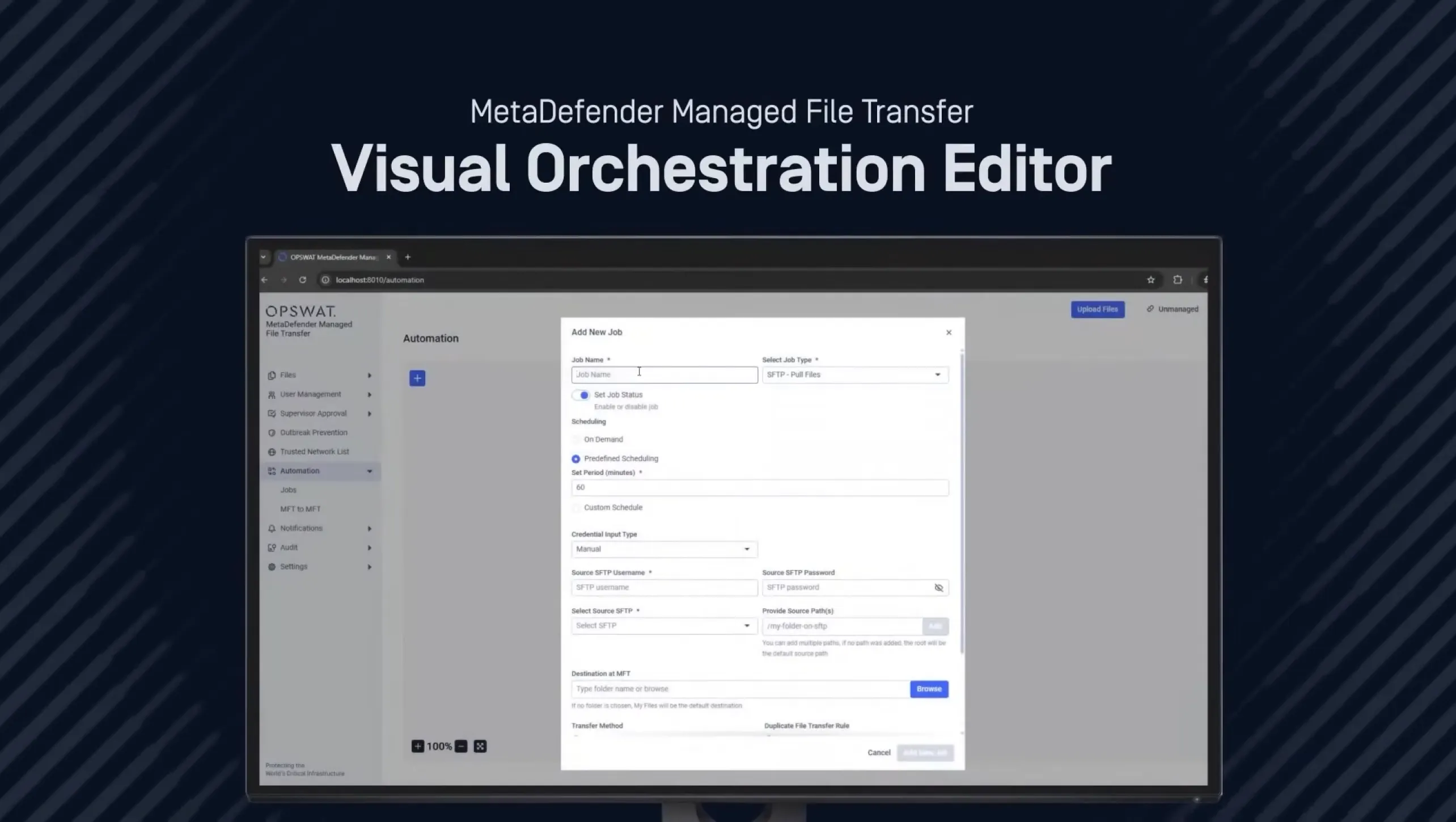
了解MetaDefender Managed File Transfer MFT) 如何透過內建的威脅防禦、政策執行、工作流程自動化,以及橫跨 IT 與 OT 環境的集中式可視性,確保檔案交換的安全性。
播放清單
4支影片- MetaDefender Managed File Transfer MFT) 產品概覽
- 透過全新的視覺化編排編輯器,Secure 傳輸 |MetaDefender MFT
- 即時示範:了解OPSWAT Managed File Transfer 如何在資訊科技領域中Managed File Transfer 活躍的惡意軟體
- 如何保護 OT 環境免受不安全的檔案傳輸影響
MFT 在 G2 2026 年春季報告中榮登MFT 領導者
高風險產業中的檔案傳輸安全
在受監管、分段式及關鍵基礎設施環境中運作的組織,必須確保檔案在系統、使用者與安全區域間的傳輸過程受到妥善保護。透過內建的檔案檢查與政策執行機制,有助於防止基於檔案的威脅干擾營運運作,或導致敏感資料外洩。
能源與公用事業
能源業者經常在企業 IT 網路與工業控制網路之間傳輸工程檔案、配置更新及營運報告。若未在傳輸節點進行檢查,基於檔案的威脅便可能滲透至 OT 環境,進而干擾營運。確保檔案在信任邊界間的傳輸安全,有助於降低網路物理風險,同時維持營運連續性。

製造業
製造商會在分段環境間交換生產檔案、韌體更新及供應商資料。只要一個檔案遭到感染,便可能在工廠系統中橫向擴散。透過實施檢查點及基於政策的路由機制,可降低因檔案型威脅導致的營運停機風險。

政府
政府機關需管理橫跨內部部門與外部合作夥伴的敏感及機密資訊。Secure 傳輸Secure 必須建立可強制執行的審批工作流程、可追溯的稽核軌跡,並在各安全域之間實施受控的路由機制,以符合國家安全及法規要求。

金融
金融機構每天都會傳輸報告、客戶資料、交易檔案及第三方文件。若缺乏集中化的可視性與基於風險的管控措施,組織將面臨合規缺口及潛在的資料外洩風險。Secure 治理有助於確保符合金融法規及資料保護法。

醫療
醫療機構會在醫療服務提供者、保險公司及雲端系統之間交換病患病歷、影像檔案及帳單資料。透過實施查閱監控、加密及有紀錄的存取控制,不僅能降低個人健康資訊(PHI)外洩的風險,同時也能確保符合《健康保險流通與責任法案》(HIPAA)及資料保護法規的要求。

Media 娛樂
Media 會在各地的製作團隊與合作夥伴之間傳輸大型影片及創意素材。內建的安全控制機制可保護智慧財產權,防止其在檔案交換過程中遭到竄改、植入隱藏式惡意軟體,或未經授權的重新散佈。

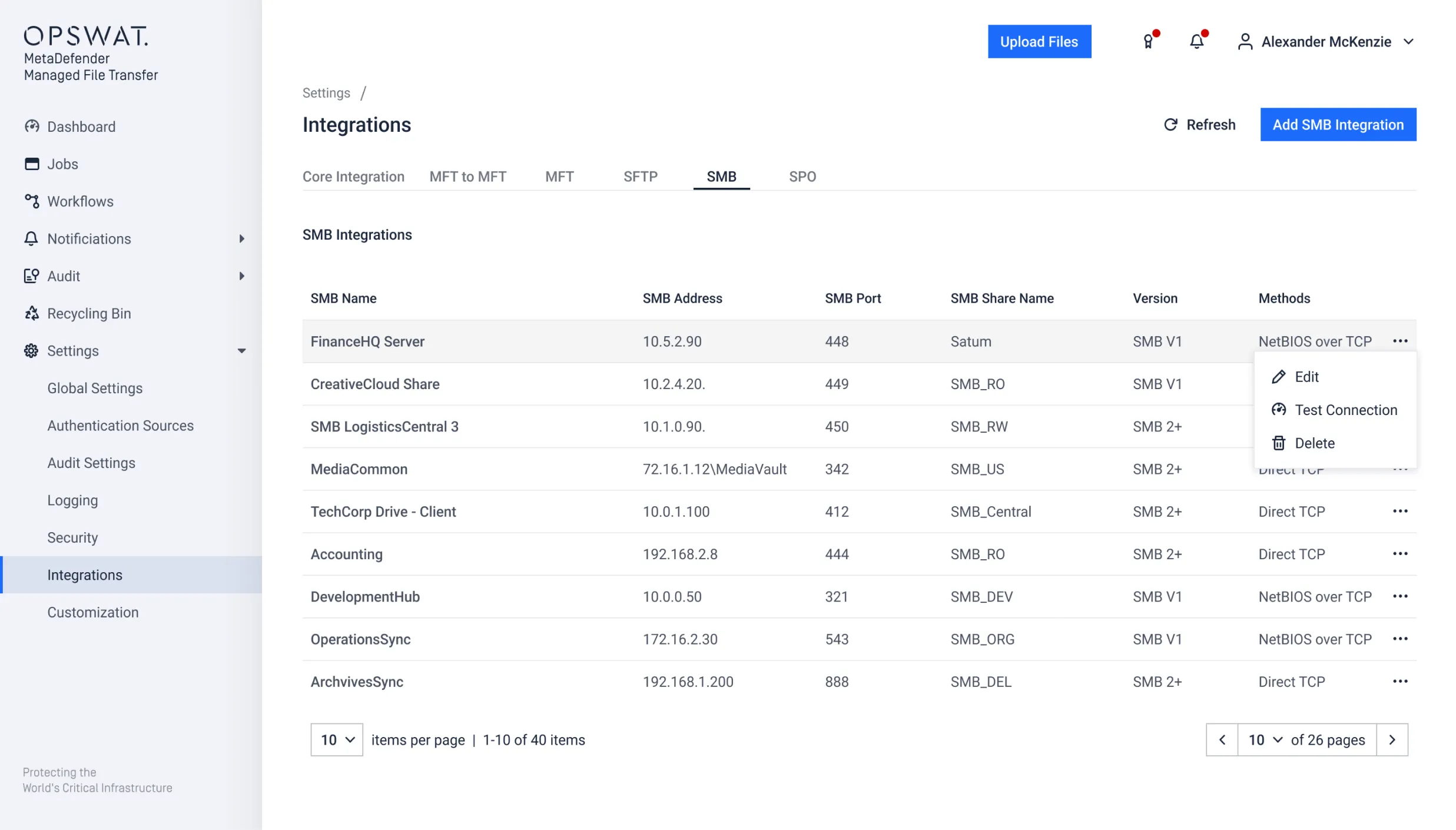
隨處部署,隨處整合
一款可擴展且全面的託管檔案傳輸解決方案,能無縫整合系統,並隨您的檔案所至而隨行。

本地
在受監管及工業網路中,Secure 與物理隔離的檔案交換Secure 。

雲端
保護橫跨 SaaS 平台、雲端儲存及分散式團隊的檔案工作流程。

混合型
在混合的 IT、OT 和雲端基礎架構中,實施一致的安全與治理措施。
客戶成功案例
專為法規遵循及
營運責任而設計
企業檔案傳輸必須符合資料保護規範、產業法規及稽核要求。OPSWAT 可執行的政策、檢查點及文件化管控措施,以支援 HIPAA、GDPR、NIS2、PCI、FISMA 及 NIST 等合規計畫。
資源

MetaDefender Managed File Transfer MFT) 產品規格書

MetaDefender Managed File Transfer MFT) 解決方案簡介
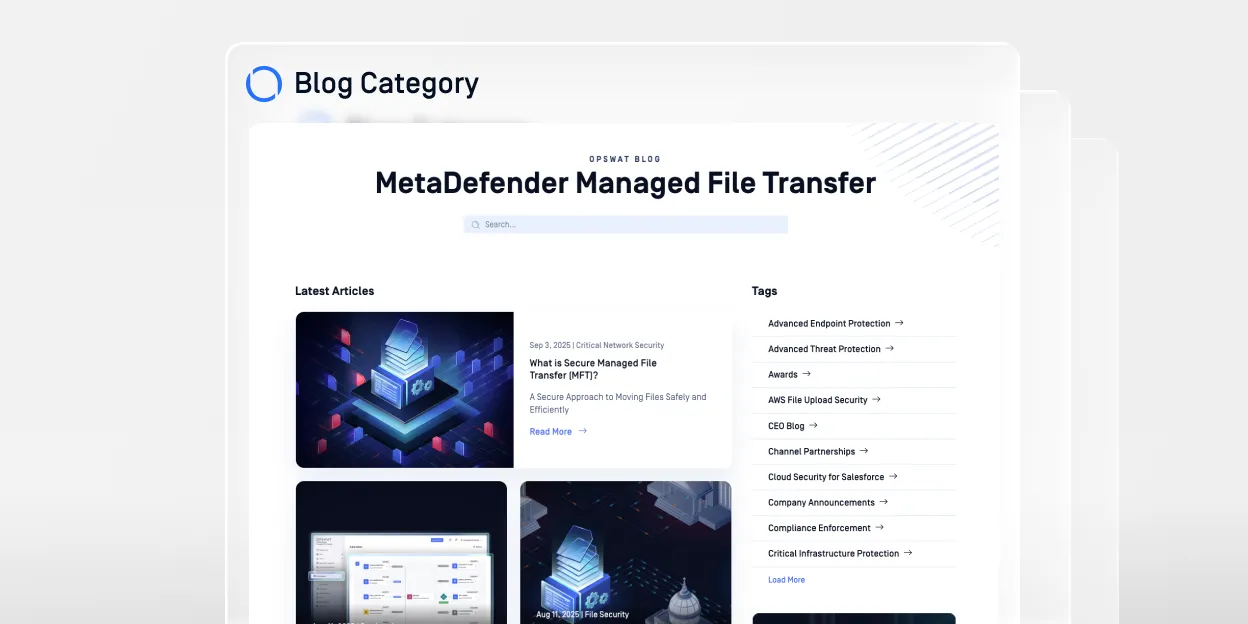
MetaDefender Managed File Transfer MFT) 部落格
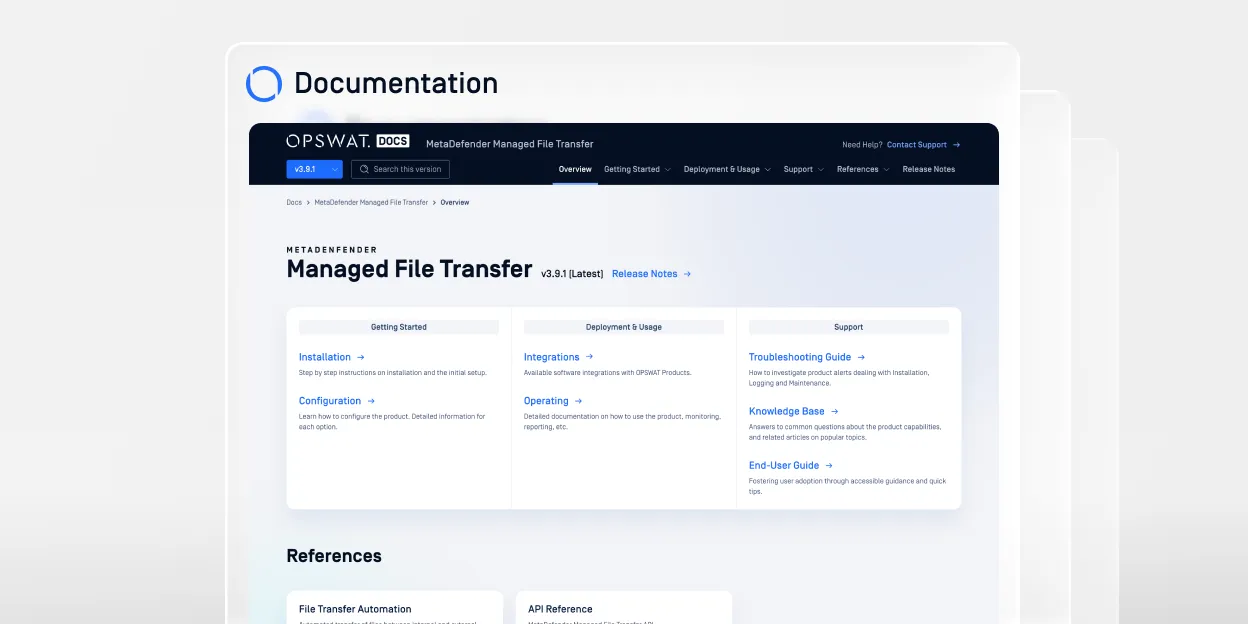
MetaDefender Managed File Transfer MFT) 文件
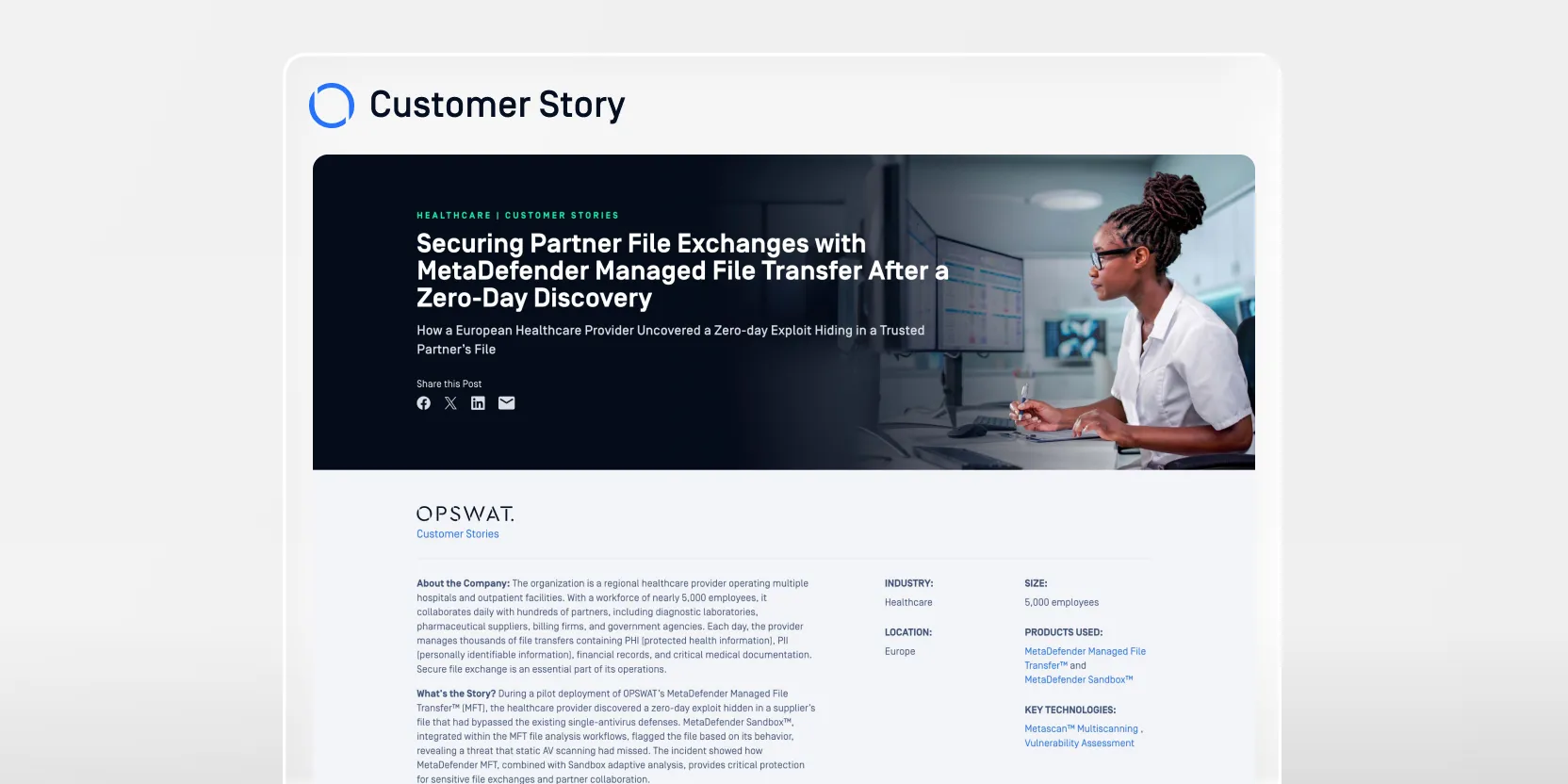
Managed File Transfer MFT)強化合作夥伴檔案交換安全防護——零時差漏洞發現後的應對措施

保護 Managed File Transfer終極指南
0 結果。請再試一次。
常見問題
當檔案在不同使用者、系統或安全區域之間傳輸時,可能攜帶隱藏的惡意軟體、嵌入式腳本或未經授權的資料。在跨域環境中——例如從 IT 網路到 OT 網路,或是從內部網路到外部合作夥伴網路——透過傳輸前的檢查(包括運用 Predictive Alin AI 進行的 AI 驅動惡意軟體偵測),有助於在已知威脅與零日威脅繞過邊界防禦並進行橫向擴散之前,及早偵測並加以防範。
基於檔案的攻擊通常始於惡意附件或遭入侵的文件。當該檔案在未經檢查的情況下於各部門、雲端平台或營運系統間傳遞時,其中嵌入的惡意程式碼便可能在新環境中執行。確保檔案傳輸的安全性,可降低此類橫向擴散的風險。
加密技術能保護傳輸中的資料免遭攔截,但並不會分析檔案內容。經過加密的惡意檔案仍可能安全地抵達目的地,並在開啟後執行。要實現有效的檔案安全,除了加密之外,還需要進行檢查並執行相關政策。
營運技術(OT)環境通常缺乏企業 IT 系統中常見的終端防護措施。若受感染的檔案滲入 OT 網路,可能會影響工業控制系統、生產線或關鍵基礎設施。確保 IT 與 OT 之間的檔案傳輸安全,有助於降低網路物理風險。
合規框架要求能夠掌握資料的存取、傳輸及儲存方式。實施具強制力的政策、建立書面批准程序,以及實施集中式稽核記錄,有助於證明對檔案移動的管控能力,並降低合規風險。
基本的檔案傳輸主要著重於將資料從一個位置移至另一個位置。Secure 治理則額外加入檢查、政策執行、存取控制及可追溯的記錄功能,以確保檔案能安全地進行傳輸,並符合組織與法規的要求。
零信任模型假設任何檔案、使用者或系統均不應被視為天生可信。透過在檔案傳輸檢查點實施檢查與政策控制,可確保每個跨越信任邊界的檔案,在被允許進入敏感環境之前均經過驗證。
組織應在以下情況下重新評估檔案傳輸的安全性:
- 擴展雲端或混合環境
- 連接 IT 與 OT 網路
- 與新的外部合作夥伴建立合作關係